The healthcare sector is one of the most vulnerable and targeted industries for cyberattacks. According to a recent report by IBM, the average cost of a data breach in healthcare was $9.23 million in 2020, the highest of any industry. And just monitor the local news: cybersecurity incidents are a continuously rising trend. Moreover, the number of security breaches in healthcare increased by 55% in 2020, affecting more than 26 million patients.
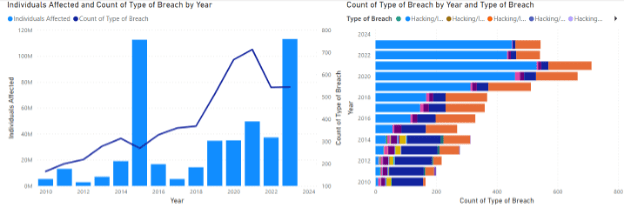
And for 2023, according to public records involving data breaches of any data breaches type involving more than 500 individual persons as reported by law to the United States, Department of Health and Human Services Office for Civil Rights have soared in 2023, will double last year’s total.
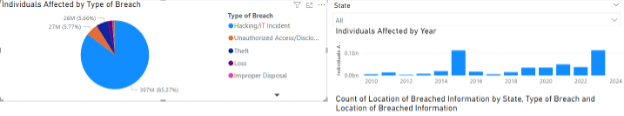
The illustrations below provide a simplified visualization via a Microsoft PowerBI report that I routinely operate to review the US HHS public data. These provide clear and unambiguous insight as to where these breaches are occurring most. Overwhelmingly its due to Hacking/IT Incident
Some of the most recent data security breaches in the healthcare sector include the following:
– In October 2023, a cyberattack on Kaiser Permanente, another large health system in the US, compromised the information of 2.8 million members and employees. The attackers gained access to Kaiser’s network through a phishing email and installed ransomware on some of its servers.
– In September 2023, several healthcare organizations reported data breaches due to the mass exploitation of a vulnerability that affected the MOVEit Transfer and MOVEit Cloud solutions (CVE-2023-34362). The largest breach involved MedStar Health, which notified 4.6 million patients of potential exposure of their data.
– In June 2023, a major data breach at HCA Healthcare, one of the largest health systems in the US, exposed the records of 11.27 million individuals. The breach was caused by a vulnerability in a third-party software used by HCA for file transfers.
– In April 2021, a ransomware attack on Scripps Health, a large health system in California, disrupted the operations of four hospitals and several outpatient clinics. The attack affected the access to medical records, appointments, lab results, and radiology reports for more than 147,000 patients.
– In March 2021, a cyberattack on a Finnish psychotherapy clinic resulted in the exposure of personal and health information of thousands of patients. The attackers also contacted some of the patients directly and demanded money to keep their data private.
– In February 2021, a hacker group known as REvil claimed to have stolen more than 600 GB of data from a French hospital group, including patient records, medical reports, invoices, and contracts. The hackers demanded a ransom of $15 million to decrypt the data and not leak it online.
Why are hackers targeting healthcare?
There are several reasons for all of the recent security breaches in healthcare, but the main one is the value of medical data. Unlike credit card information or passwords, which can be changed or canceled, medical records contain sensitive and permanent information such as personal details, diagnoses, prescriptions, insurance information, and more. This data can be used for identity theft, fraud, blackmail, or even espionage.
Another reason is the lack of adequate security measures and awareness in healthcare organizations. Many healthcare providers use outdated or legacy systems that are not patched or updated regularly, leaving them exposed to vulnerabilities and exploits. Additionally, many healthcare workers are not trained or informed about the best practices for cybersecurity, such as using strong passwords, encrypting data, or avoiding phishing emails.
How can healthcare organizations protect themselves from cyberattacks?
There is no silver bullet solution, but there are some steps that can help reduce the risk and impact of security breaches:
- Conduct regular risk assessments and audits to identify and address any gaps or weaknesses in the security posture. (https://quisitive.com/solutions/integration-consulting/security/cloud-security-assessement/)
- Implement a robust security framework that follows the standards and guidelines of industry bodies such as HIPAA, NIST, or ISO. (Security management | Quisitive)
- Invest in security tools and technologies that can detect, prevent, and respond to cyber threats, such as firewalls, antivirus software, encryption software, backup systems, etc (https://quisitive.com/solutions/integration-consulting/digital-workplace/microsoft-365-security-assessment/) or Microsoft Sentinel Quick Start | Quisitive
- Educate and train staff on cybersecurity awareness and best practices, such as how to recognize and report suspicious activities, how to handle sensitive data, how to use secure communication channels, etc.
- Develop and test a security incident response plan that outlines the roles and responsibilities of different stakeholders, the procedures and protocols for handling a breach, the communication and notification strategies, etc. (Security management | Quisitive)
Cybersecurity is not a one-time project, but an ongoing process that requires constant vigilance and adaptation. By taking these steps, healthcare organizations can improve their security posture and resilience against cyberattacks.
At Quisitive, we are here to help…
Pick any or all the topics on the suggested list I have provided (above) and ask us to meet with you. We have solutions that solve these issues built upon the strength of the Microsoft M365 E5 and Azure Advanced Security Stack, as well as the experience of having performed thousands of past projects. Our Spyglass team partner with your team to help with hands-on services to advise, design, implement, optimize, and manage your Microsoft Security Stack in Office 365, Azure and Dynamics and greatly improve your overall security posture while improving your users’ IT experience. (Security management | Quisitive)
We can also monitor your environment 24x7x365 with our MDR/XDR services (https://quisitive.com/managed-services/spyglass/managed-detection-response/)
Please reach out to us if you have any questions (Security | Quisitive)
Until next time,
Ed

;)



