As COVID dramatically shifted how people work over the last long year, many businesses have accelerated their adoption of cloud services to support collaboration and productivity from virtually anywhere, but namely from home.
Over the past year, our Spyglass Security & Compliance team has witnessed explosive increases in the adoption of applications such as Microsoft Teams, Zoom, Hangouts, and many other apps. Of key interest for this post, is the “other apps” mention. How our workforce personnel access company resources warrants even more focus for businesses, and here’s why. While legitimate application use (e.g., Teams, Zoom, Hangouts) has accelerated and enabled employees to be productive remotely and remain connected to co-workers despite work from home mandates, attackers have focused on application-based attacks to gain unauthorized access to your data. This is where the “other apps” need to be scrutinized carefully, as some could be malicious.
While much of our workforce personnel are familiar with attacks focused on users, such as email phishing or credential compromise, application-based attacks such as consent phishing is another threat vector to be aware of. Today we wanted to share one of the ways application-based attacks can target the valuable data your organization cares about, and what you can do today to stay safe. Our Spyglass services team works with our clients to help continually improve security posture while enabling more collaboration (securely). Functionally, we provide assistance to identify threats such as consent-phishing among many and implement protections for them, in order to reduce the risks of such attacks.
However, when we meet many new clients through our award-winning M365 Security Assessment, we consistently identify malicious apps interacting with client Office 365 environments due to poorly configured (or unconfigured) security protections and also due to successful attacks involving consent-phishing attacks carried out on victim users. Below is an illustration of one such (and common) consent-phishing attack. Notice that an application named Email from a publisher name Test, was consented by a user and is actively interacting via OAuth with Office 365 targeting contacts, data, and other potentially sensitive information.
Consent phishing: An application-based threat to keep an eye on
Developers create apps that integrate user and organizational data from cloud platforms to enhance and personalize their experiences. Cloud platforms are rich in data but in turn have attracted malicious actors seeking to gain unwarranted access to this data. One such attack is consent phishing, where attackers trick users into granting a malicious app access to sensitive data or other resources. Instead of trying to steal the user’s password, an attacker is seeking permission for an attacker-controlled app to access valuable data.
While each attack tends to vary, the core steps usually look something like this:
- An attacker registers an app with an OAuth 2.0 provider, such as Azure Active Directory.
- The app is configured in a way that makes it seem trustworthy, like using the name of a popular product used in the same ecosystem.
- The attacker gets a link in front of users, which may be done through conventional email-based phishing, by compromising a non-malicious website, or other techniques.
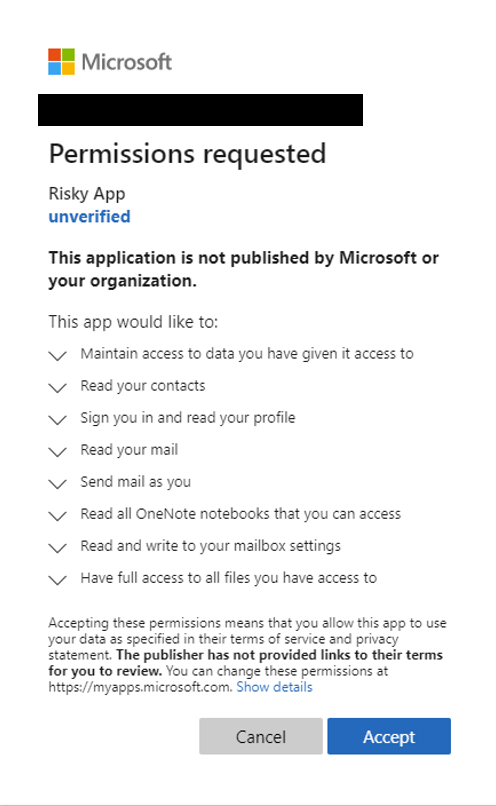
- The user clicks the link and is shown an authentic consent prompt asking them to grant the malicious app permissions to data.
- If a user clicks accept, they will grant the app permissions to access sensitive data.
- The app gets an authorization code which it redeems for an access token, and potentially a refresh token.
- The access token is used to make API calls on behalf of the user.
If the user consents (or accepted the app’s requested access, then the attacker can gain access to their mail, forwarding rules, files, contacts, notes, profile and other sensitive data and resources.
Guidance to protect your organization
With Microsoft’s integrated security stack, we are able to identify and take measures to remediate malicious apps by disabling them and preventing users from accessing them. In some instances. Microsoft has also taken legal action to further protect its customers. While attackers will always persist, there are steps you can take to further protect your organization. Some best practices include the following:
Educate those in your organization on consent phishing tactics:
- Check for poor spelling and grammar. If an email message or the application’s consent screen has spelling and grammatical errors, it’s likely to be a suspicious application.
- Keep a watchful eye on app names and domain URLs. Attackers like to spoof app names that make it appear to come from legitimate applications or companies but drive you to consent to a malicious app. Make sure you recognize the app name and domain URL before consenting to an application.
- Check out Attack Simulator and Training or ask Quisitive to show you how it works or implement it for you
Promote and allow access to apps you trust:
- Promote the use of applications that have been publisher verified. Publisher verification helps admins and end-users understand the authenticity of application developers. Over 660 applications by 390 publishers have been verified thus far.
- Configure application consent policies by allowing users to only consent to specific applications you trust, such as application developed by your organization or from verified publishers.
Educate your organization on how our permissions and consent framework works:
- Understand the data and permissions an application is asking for and understand how permissions and consent works within Office 365.
- Ensure administrators know how to manage and evaluate consent requests.
- Audit apps and consented permissions regularly in your organization to ensure applications being used are accessing only the data they need and adhering to the principles of least privilege.
The increased use of cloud applications has demonstrated the need to improve application security. For additional best practices and safeguards review Microsoft’s Detect and Remediate Illicit Consent Grants in Office 365 and Five steps to securing your identity infrastructure which provide additional good guidance based on best-practices.
Hope this helps. Stay Safe.
Until next time,
Ed

;)



