In a world where cybersecurity threats are constantly evolving, staying one step ahead is no easy feat. Security teams often find themselves overwhelmed by the ever-changing tactics, techniques, and procedures employed by cybercriminals. To combat this, organizations are shifting their focus towards building a robust security program that relies on strategy rather than reacting tactically to every threat that arises.
In this blog, we’ll explore five essential priorities for security teams to reduce risk and fortify their organization’s security posture:
Priority 1: Framework Alignment
Achieving seamless alignment with industry-standard security frameworks is the cornerstone of a resilient security program. These frameworks provide a structured approach to security, helping organizations meet compliance requirements and establish a solid foundation for protection. However, navigating the complex landscape of security frameworks can be a challenge that demands your utmost attention. Ensuring that your security strategy aligns with these frameworks is the first step in building a formidable defense.
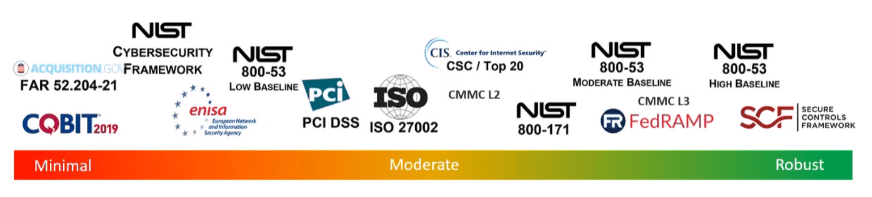
“66% of cybersecurity leaders are not highly confident in their current strategies for evaluating and mitigating major cyber risk, highlighting the need for a robust framework” (Critical Start Cyber Risk Landscape Peer Report – Critical Start). Choosing the right security framework for your business is important because it will provide guidelines, standards, and best practices to reduce risk. This framework will lead to better planning, emulation, and response to adversarial threats across your organization.
Priority 2: Simplifying Security Architecture
Complexity can be the enemy of efficiency in the realm of security. The quest for an adaptive and effective security infrastructure begins with simplification. A convoluted architecture not only hampers response times but also increases the risk of overlooking critical vulnerabilities. By simplifying your security architecture, you unlock its true potential, making it easier to manage and maintain while reducing the likelihood of security gaps.
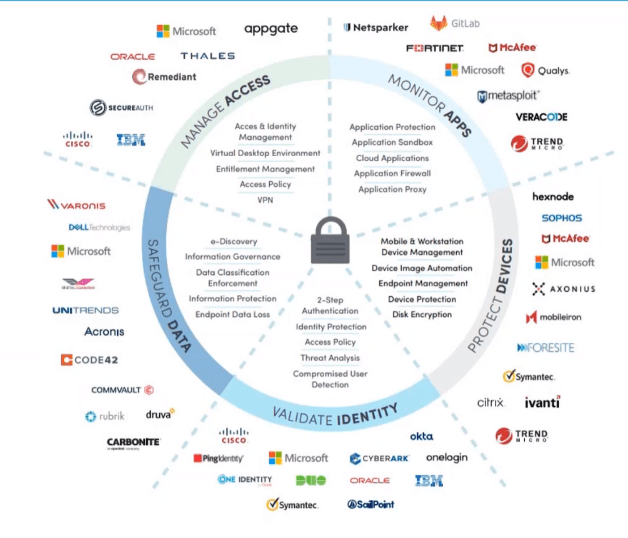
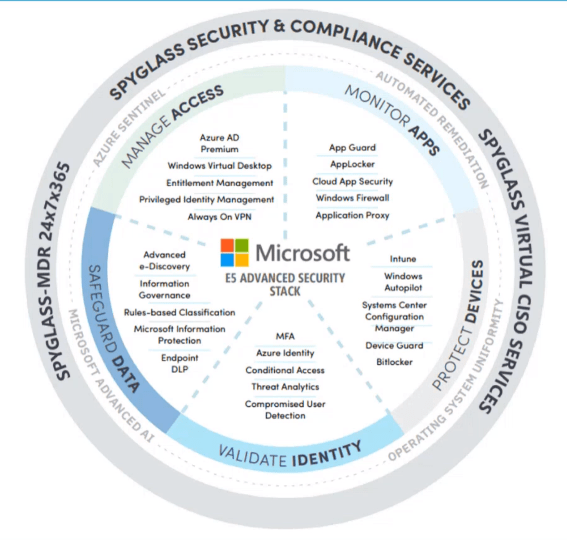
Combining and integrating security tools is a necessity to ensure that your organization doesn’t have duplicate tools – we want to ensure that you’re getting the full potential of each tool. “67% of organizations experienced a cyber incident despite having traditional threat-based security tools in place” (Critical Start Cyber Risk Landscape Peer Report – Critical Start). Since having too many disparate tools can lead attackers to move through your security environment, it is best to consolidate tools and close those gaps.
Priority 3: Endpoint Security
The rapid rise of remote work and the proliferation of endpoints have shifted the frontline of defense to endpoint security. Securing each device within your organization is paramount to prevent cyber threats from gaining a foothold. As remote work becomes the new norm, protecting these endpoints becomes an essential component of your security strategy.
- EDR is necessary for full visibility – this is the best place for detection, investigation, & response
- Endpoint detects threats and utilizes advanced analytics to pick up fraud or breaches
- Ensure full deployment of endpoint controls
- Not just EDR, but also EPP, patching, vulnerability management, and backup
- Allows for conditional access and limited privilege to stay secure
Microsoft Defender for Endpoint includes:
- Unified security tools and centralized management
- Next-generation anti-malware
- Attack surface reduction rules
- Device control (such as USB)
- Endpoint Firewall
- Network protection
- Web control/category-based URL blocking
- Device-based conditional access
- Controlled folder access
- APIs, SIEM Connector, custom threat intelligence
- Application control
Priority 4: Vulnerability Management
In a threat landscape that never stands still, identifying, prioritizing, and mitigating vulnerabilities is a continuous endeavor. The success of your security strategy hinges on how effectively you manage this process. Vulnerability management ensures that potential weaknesses are addressed promptly, reducing the attack surface and minimizing the risk of exploitation.
When more than half of the vulnerabilities in security environments are an eight or higher (or considered critical), you’re going to have a hard time establishing a level of best practice, procedure, or process around vulnerability mitigation and patching. If you’re truly focused on vulnerability management, it’s essential to prioritize those vulnerabilities to better tackle them:
- Develop vulnerability management programs with executive alignment and support
- Establish SLAs for priority vulnerabilities
- Identify and document system owners and using a risk registry to track patching exceptions
- Integrate vulnerability management with other security solutions and processes for a holistic approach
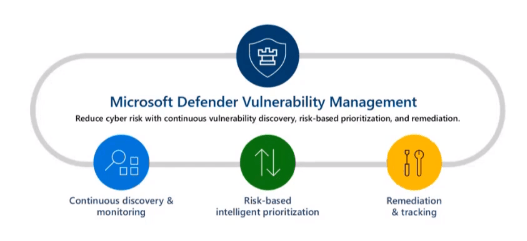
Microsoft Defender Vulnerability Management (Defender for Endpoint P2 or M365 E5) provides advanced capabilities including:
- Defender for Servers, powered by Qualys Scanner
- Continuous asset discovery and monitoring
- Risk-based intelligent prioritization
- Remediation guidance and assignment tracking
- Dashboards, metrics, and performance measurements (scoring)
Priority 5: 24×7 Monitoring Capabilities
Cyber threats don’t abide by regular business hours. Establishing vigilant 24×7 monitoring capabilities is no longer a luxury but a necessity for early threat detection and rapid response. Whether it’s a data breach, a malware infection, or a network intrusion, the ability to monitor your environment around the clock is crucial to minimizing the impact of security incidents.
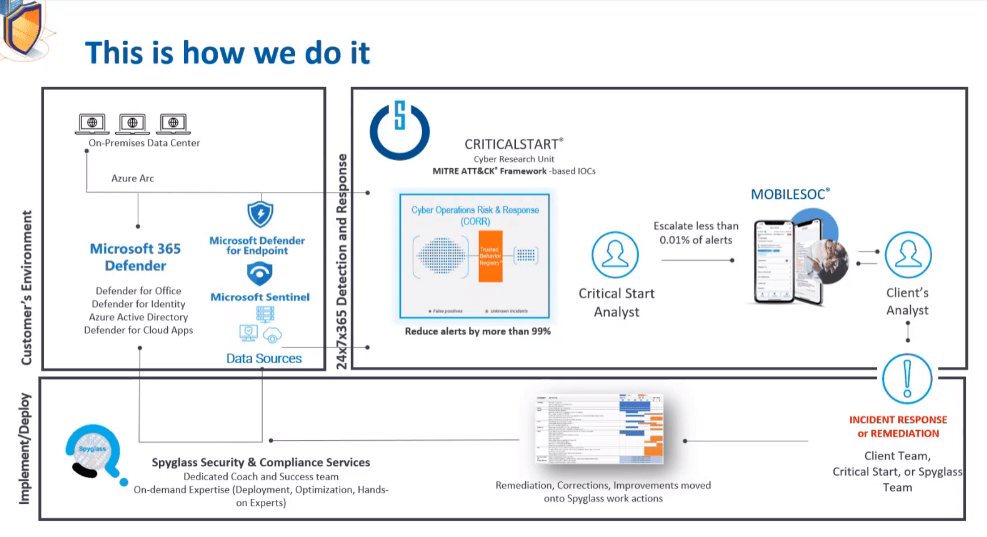
“93% of organizations plan to offload specific segments of cyber risk reduction workstreams or projects to security service providers within the next two years” (Critical Start Cyber Risk Landscape Peer Report – Critical Start). 24×7 monitoring also ensures that every security alert is resolved and helps to establish and require metrics and SLAs. The image below illustrates how Quisitive and Critical Start come together to keep your organization secure.
In conclusion, as the threat landscape continues to evolve, it’s imperative that security teams take a proactive approach to protect their organizations. By aligning with security frameworks, simplifying security architecture, prioritizing endpoint security, mastering vulnerability management, and implementing 24×7 monitoring capabilities, you can reduce risk and build a robust security program that can withstand the challenges of today’s digital world. Remember, it’s not about playing catch-up with cyber threats; it’s about staying ahead of the game.

;)